Multiple U.S. Government agencies are urging Windows 10 users to update as soon as possible
GETTY IMAGES
When the technical director of the U.S. National Security Agency (NSA) Cybersecurity Directorate, and the Department of Homeland Security’s Cybersecurity & Infrastructure Security Agency (CISA), both urge Windows 10 users to take action and update as soon as possible, you might suspect that something serious has happened.
You would be right.
As I predicted in an article called “New Windows 10 ‘Extraordinarily Serious’ Security Warning For 900 Million Users,” published early yesterday morning, the monthly Patch Tuesday update from Microsoft disclosed a particularly concerning vulnerability in Windows 10.
Even before Microsoft itself disclosed the details of CVE-2020-0601, a Windows CryptoAPI spoofing vulnerability, the NSA had confirmed the importance of both the flaw and the fix. Anne Neuberger, director of the NSA Cybersecurity Directorate, warned that the issue “makes trust vulnerable.”
Indeed, it was the NSA itself that discovered the vulnerability and reported it to Microsoft. This is, Neuberger confirmed, the first time that the NSA had publicly disclosed a vulnerability to a software vendor.
Now another U.S. Government agency has boarded the vulnerability warning battle-bus and urged Windows 10 users to apply the Patch Tuesday updates as soon as possible. CISA, via the National Cyber Awareness System, has published an alert titled “Critical Vulnerabilities in Microsoft Windows Operating Systems.” This calls the Windows CryptoAPI vulnerability a “critical weakness” and warns that an attacker could remotely exploit this, and other vulnerabilities fixed by the Patch Tuesday update, to “decrypt, modify, or inject data on user connections.”
What is CVE-2020-0601?
The vulnerability affects all systems running Windows 10 in 32 or 64-bit versions. The CISA alert explains that it allows Elliptic Curve Cryptography (ECC) certificate validation to bypass the trust store. In other words, this means that malicious software could masquerade as legitimate software that has been authenticated and signed by a trusted source; malware detection could be negatively impacted as a result. Furthermore, browsers that rely upon Windows CryptoAPI could be fooled by a maliciously signed digital certificate and so no warnings would be issued if a threat actor were to then decrypt data or inject malicious data.
CVE-2020-0601 can be exploited to undermine Public Key Infrastructure (PKI) trust, according to Neal Ziring, technical director of the NSA Cybersecurity Directorate. “This kind of vulnerability may shake our belief in the strength of cryptographic authentication mechanisms,” Ziring said, “and make us question if we can really rely on them.”
How serious is this Windows 10 vulnerability?
While there has been some debate amongst infosecurity professionals online as to the extent to which this vulnerability could be exploited, with some even suggesting it is something of an NSA PR stunt, most agree that CVE-2020-0601 cannot be ignored. “This vulnerability may not seem flashy, but it is a critical issue,” Ziring said, “trust mechanisms are the foundations on which the internet operates, and CVE-2020-0601 permits a sophisticated threat actor to subvert those very foundations.”
“While it is relatively uncommon for a vulnerability of this severity to make it through the NSA’s Equities process and not be weaponized and kept secret for its offensive capabilities,” Chris Hass, the director of information security and research at Automox, and a former NSA security analyst, said, “it does allude to a possible shift in mentality.” That being as a result of bad publicity with recent ransomware infections that were made possible by EternalBlue, a leaked NSA exploit. ” If an attacker could spoof a cert to look like a trusted vendor, they would likely bypass most security controls present in the organization, giving them free rein to do whatever they wanted,” Hass said, “this doesn’t just affect signatures; it will also affect conviction rates of AI-based models due to the fact most AI-models use digital signatures to some capacity in weighing whether a file is malicious or not.”
“The vulnerability is only rated as important, but there have been many examples of CVEs that were only rated as important being exploited in the wild,” Todd Schell, senior product manager at Ivanti said, “due to the nature of this vulnerability we would urge companies to treat this as a top priority this month and remediate quickly.”
When thinking in terms of likely attack scenarios, Pratik Savla, a senior security engineer at Venafi, said that “if attackers disguise a malicious executable binary, so it looks like a Windows system binary, it can remain undetected by anti-virus. This could allow attackers to blend in and install it, and they get the command and control channel re-established on reboot.”
In a technical advisory document, the NSA explains how the vulnerability could enable the invalidation of trust in HTTPS connections, signed files, and emails as well as signed executable code launched as user-mode processes. It further warns that “Remote exploitation tools will likely be made quickly and widely available,” hence the urgency required in applying the Patch Tuesday fix.
While there are no known exploitations of the vulnerability in the wild at this stage, the NSA is right in warning that things are likely to change pretty quickly now that the vulnerability disclosure has been made public. “Because patches have been publicly released,” CISA said, “the underlying vulnerabilities can be reverse-engineered to create exploits that target unpatched systems.”
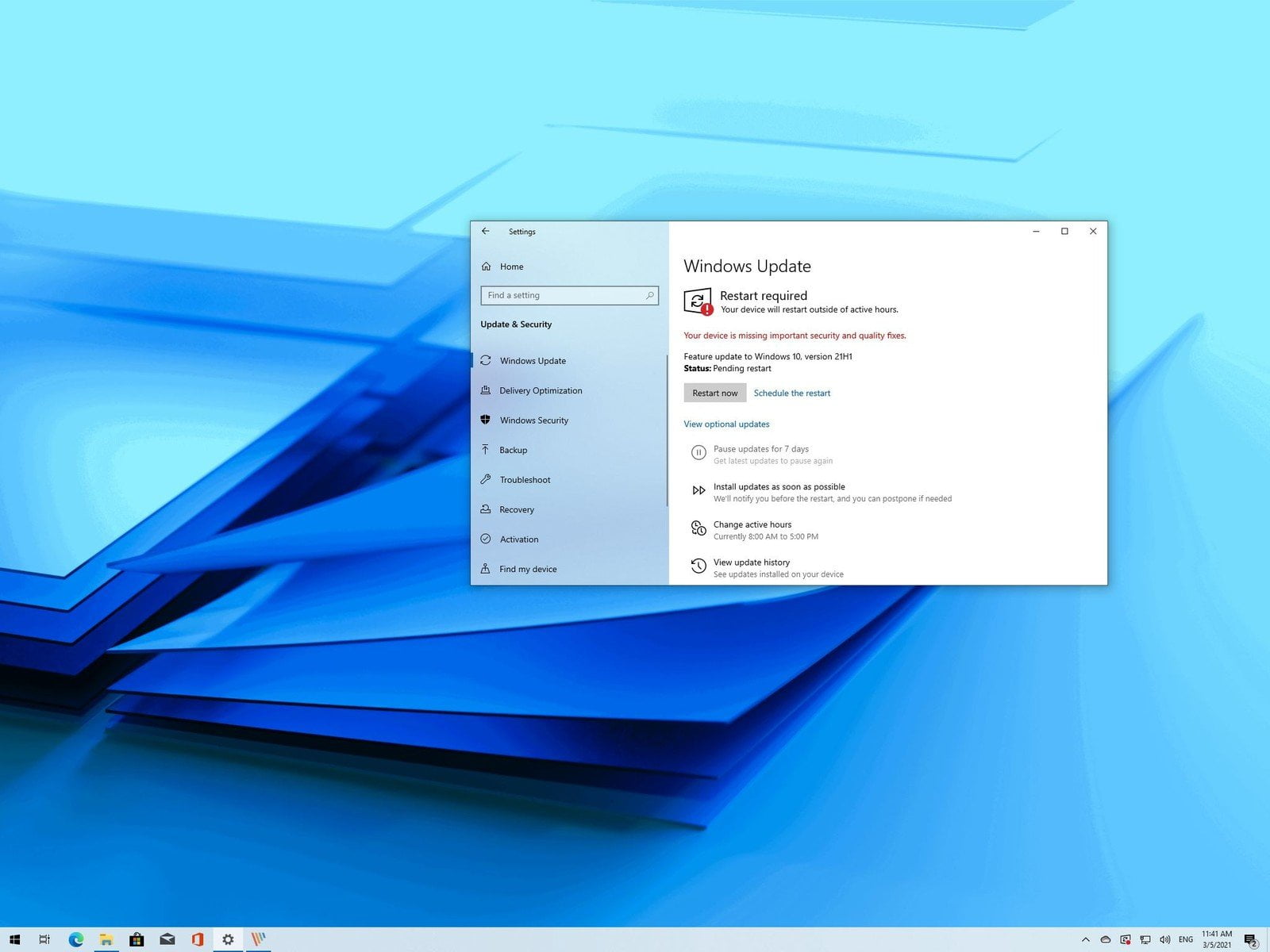
Patch your Windows 10 systems, and patch them now
The advice of the security professionals I have spoken to, and U.S. Government agencies such as CISA and the NSA for good measure, remains the same as I gave yesterday morning: don’t defer this particular Windows Patch Tuesday update, apply it as soon as you possibly can.
As Tim Mackey, principal security strategist within the Synopsys CyRC (Cybersecurity Research Center), said: “there are times when it’s reasonable to defer a patch, but deferring the patch for CVE-2020-0601 isn’t one of them.”
The exploit clock is now ticking.
[“source=forbes”]